So i’ve been hosting a modded Minecraft server for my friends and me on weekends. While it’s been a blast, I’ve noticed that our current setup using LAN has its limitations. My friends have been eagerly waiting for their next “fix” (i.e., when they can get back online), and I’ve been replying with a consistent answer: this Friday.
However, exploring cloud providers to spin up a replica of my beloved “Dog Town” Server was a costly endeavor, at least for a setup that’s close to my current configuration. As a result, I’ve turned my attention to self-hosting a Minecraft server on my local network and configuring port forwarding.
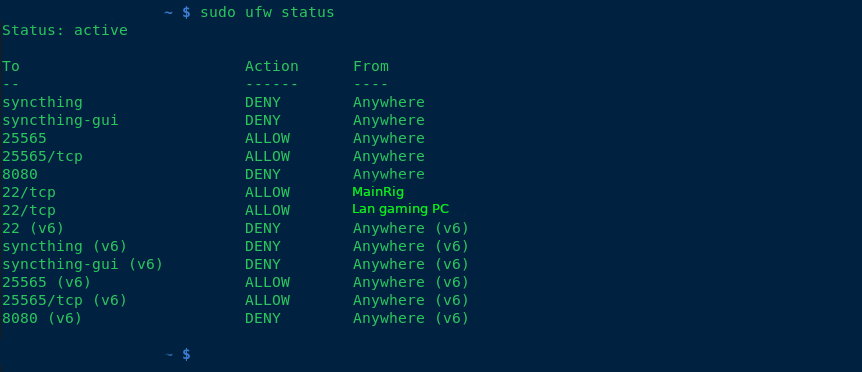
To harden my server, I’ve implemented the following measures:
- Added ufw (Uncomplicated Firewall) for enhanced security.
- Blocked all SSH connections except for the IP addresses of my main PC and LAN rig.
- Enabled SSH public key authentication only.
- Rebuilt all packages using a hardened GCC compiler.
- Disabled root access via
/etc/passwd. - Created two users: one with sudo privileges, allowing full access; the other with limited permissions to run a specific script (
./run.sh) for starting the server.
Additionally, I’ve set up a fcron job (a job scheduler) as disabled root, which synchronizes my Minecraft server with four folders at the following intervals: 1 hour, 30 minutes, 10 minutes, and 1 day. This ensures that any mods we use are properly synced in case of issues.
any suggestions of making the computer any more secure, aswell as backup solutions? thanks!
–added note, what hostnames do you guys call your servers? I used my favorite band albums and singles for hostnames.
If you wanted to go overboard, don’t even make the server accessible publicly. Distribute keys to a Wireguard network that is accessible publicly. Mandate your players obtain keys from you to play.
Even faster – tailscale. For a cheeky way to play with your friends make a burner account with a shared login to get on the same tailnet for free. On the endpoints, turn off tailscale-ssh and any of their other “features” you don’t need.
IMO the biggest attack vector there would be a Minecraft exploit like log4j, so the most important part to me would make sure the game server is properly sandboxed just in case. Start from a point of view of, the attacker breached Minecraft and has shell access to that user. What can they do from there? Ideally, nothing useful other than maybe running a crypto miner. Don’t reuse passwords obviously.
With systemd, I’d use the various Protect* directives like ProtectHome, ProtectSystem=full, or failing that, a container (Docker, Podman, LXC, manually, there’s options). Just a bare Alpine container with Java would be pretty ideal, as you can’t exploit sudo or some other SUID binaries if they don’t exist in the first place.
That said the WireGuard solution is ideal because it limits potential attackers to people you handed a key, so at least you’d know who breached you.
I’ve fogotten Minecraft servers online and really nothing happened whatsoever.
Removed by mod
Yeah, that didn’t stop it from pwning a good chunk of the Internet: https://en.wikipedia.org/wiki/Log4Shell
Removed by mod
You should isolate it. Use Docker or Podman or any container solution to put the server in a container for isolation from the main system. Any external directory outside the container the server won’t write to should be in read only mode.
If the server is only for your friends. Stop exposing your network to the public and instead use VPNs.
Regarding VPNs, I wish this was an easier way of doing it. Unfortunately it requires all friends to be tech savvy enough to understand why a vpn is necessary.
Why would they need to understand? Just tell them that it’s needed to play on the server and set it up for them. Whenever they want to play, they can use the VPN.
Use wg-easy has a dead simple web ui then just send your friends a link to wireguard downloads page and a copy of the their .conf file it has an import button.
I just tell them its the app you need to connect to my network. True enough and I’ve never had anyone have much issues.
Fellow Gentoo user! Kudos.
Have you tried using an audit tool? Check out https://cisofy.com/lynis/
Is this machine sitting in your LAN, or on its own firewalled off network with a DMZ? No matter how secure it is, you don’t want it on the same network as the machine you do your taxes on.
A good poor mans option is to get a pfsense box with 3 NIC’s. One for WAN, one for LAN, and one for the machine you publicly host with.
Setup firewall rules so that LAN can reach the MC host on needed ports, but not the other way around.
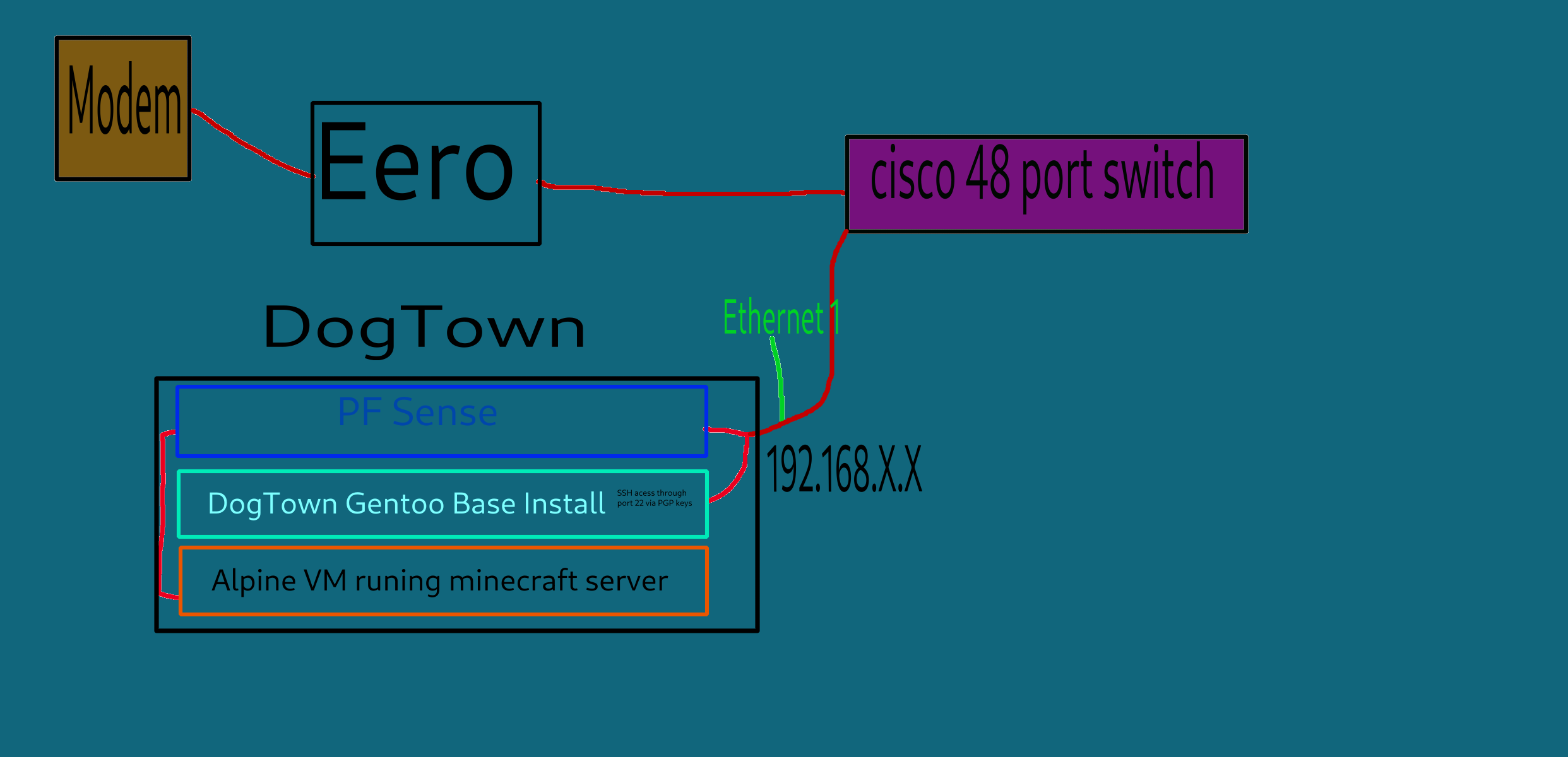
Currently the plan is to use my 48 port cisco switch and put the server on a separate vlan. I assume that is very similar to your pfsense solution? Please correct me if im wrong
You’re adding attack surface by keeping them separated only by vlan. VLAN hopping exploits exist, especially in older firmware, ESPECIALLY on EoL units.
Pfsense is a proper router/firewall built on one of the most hardened networking stacks on the planet. Plus it catches regular software updates, no matter how old your hardware is. You can run it on an old PC with a cheap quad gigabit nic card from eBay if you’d like.
If I might ask, what do you have handling your inter-vlan routing/firewall? Is it the same box you use to handle the firewall/routing between your WAN and LAN?
currently my setup is a dsl modem that goes, to my router/WAP which is a eero, that i plan to eventually replace with a Banna pi R4 which will run openwrt. but as of now the eero goes to my 48 port in my server room, and i have all my computer jacked into that. so to answer your question, my firewall is handled by my router and individual local rules by my machines. im kinda new to self hosting and port forwarding and pfsense looks pretty useful. i know pfsense is based on freebsd so is that a big plus vs openwrt?
please let me know, what some potential solutions could be.
Pfsense is a lot more feature rich than openWRT, especially when it comes to firewall features. Personally I just use openwrt to run my access points.
I would replace that eero unit with an old dell optiplex with pfsense, and forego trying to virtualize PFSense.
Not sure what hardware is in that eero, but if you wanted to keep it as just a basic AP, that isn’t a bad plan.
After that get a second optiplex for publicly hosted stuff. Keep that on a separate port on your PFSense machine, completely firewalled off from the rest of your network via pfsense, only allowing traffic from LAN to your server.
Physically separating your internal network, and publicly hosted services, as much as possible is the goal.
If you can only afford one new piece of hardware, I’d get the pfsense box, and set it up as a wireguard VPN server, disabling the direct port forwards to the VM running Minecraft. Though your friends would need to install a VPN client, and youd have to provide config files.
A used optiplex on eBay usually isn’t much more money to get up and running than most Linux SoC’s after all the adapters and kit is purchased, and they’re usually specced out way better.
Actually if you wanted to do physical DMZ separation, and wireguard you’d really be doing good, but that’s probably a little paranoid.
also follow up question, alot of people are saying to make the mine-craft server run in a vm for host isolation. So what if i spun up 2vm’s
#1 would be a virtualized instance of pf sense, i would then have ethernet 1 on dogtown give internet to the base gentoo install, then have a Ethernet 2 go into PF sense, which will then have firewall rules to restrict access to the vm minecraft server. would that work? or is there somthing im misisng?
Diagram added
So the local machine doesn’t really need the firewall; it definitely doesn’t hurt, but your router should be covering this via port forwarding (ipv4) or just straight up firewall rules (ipv6).
You can basically go two routes to reasonable harden the system IMO. You can either just set up a user without administrative privileges and use something like a systemd system level service to start the server as that user and provide control over it from other users … OR … if you’re really paranoid, use a virtual machine and forward the port from the host machine into the VM.
A lot of what you’re doing is … fine stuff to do, but it’s not really going to help much (e.g. building system packages with hardening flags is good, but it only helps if those packages are actually part of the attack surface or rather what’s exposed to the remote users in someway).
Your biggest risk is going to be plugins that aren’t vetted doing bad things (and really only the VM or using the dedicated user account provides an insulation layer there – the VM really only adds protection against privilege escalation which is pretty hard to pull off on a patched system).
My advice for most people:
- Make a new user on the system to run each game you want to run
- Run the game using systemd and that user
- Use something like kopia + the root user’s crontab (easier than systemd timers, but systemd timers also work) to backup the files on disk
For Minecraft in particular, to properly back things up on a busy server you need to disable auto save, manually force save, do the backup and then enable auto save again after your backup. Kopia can issue commands to talk to the server to do that, but you need a plugin that can react to those commands running on the server (or possibly to use the server console via stdin). Realistically though, that’s overkill and you’ll be just fine backing up the files exactly as they are periodically.
Kopia in particular will do well here because of its deduplication of baked up data + chunking algorithm that breaks up files. That has saved me a crazy amount of storage vs other solutions I’ve tried. Kopia level compression isn’t needed because the Minecraft region files themselves are already highly compressed.
If you are port forwarding. I recommend not exposing it on the default port of 25565 and instead expose it as a random port. Then, assuming you have a domain name, create an SRV record that points to your IP and port. This will cut down on the drive by scanners who scan by ports, but won’t totally eliminate it. If you do use the SRV record, your friends won’t even notice there’s a different port.
I am not sure if there is a good way to do it without scripting, and a router that would allow for taking variable input from an external script. But theoretically if the router would support it, you could script a port change at times there are no one on the server.
Essentially the server port is in a text file, you could use some command line utilities, and write a script leveraging something like sed to change the port in place.
But I am overcomplicating it. lol
Whitelist and an autobackup mod
Totally agree with the mentions of Wireguard and Tailscale. They make this super easy. Have done exactly this myself before, for the same use case.
However at the time, i had to change something in the server-properties config file in order for it to work properly. Minecraft servers still authenticate users when hosting yourself (afaik). This however isnt possible over a mesh netowrk like wireguard/tailscale. I simply had to change a boolean value of the line called something like, server-online, or online-mode…
Best of luck!
i think i may go with wire guard, do you know of any good videos or tutorials? i found this, https://www.digitalocean.com/community/tutorials/how-to-set-up-wireguard-on-ubuntu-20-04
I recommend using a docker container, they make the whole thing painless and easy.
I think the Linuxserver.io one is what I used from memory.
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
Fewer Letters More Letters AP WiFi Access Point IP Internet Protocol LXC Linux Containers VPN Virtual Private Network
4 acronyms in this thread; the most compressed thread commented on today has 11 acronyms.
[Thread #963 for this sub, first seen 10th Sep 2024, 14:45] [FAQ] [Full list] [Contact] [Source code]
Hey! What is that color scheme? I love it.
its flat theme
Thanks!










