Mathematician warns NSA may be weakening next-gen encryption::Quantum computers may soon be able to crack encryption methods in use today, so plans are already under way to replace them with new, secure algorithms. Now it seems the US National Security Agency may be undermining that process
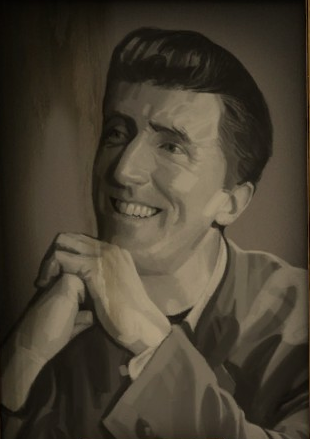
Daniel Bernstein (djb) is a well known and respected cryptography researcher so his claim carries a lot of weight. It’s also worth noting that NIST didn’t invent these post quantum encryption algorithm. Instead, they run a competition and select a winner. Djb’s algorithm got a second place, so people were wondering if he’s just being salty about it, though if NIST were really compromised, it’s not hard to imagine they’ll select a weaker algorithm as the winner instead. NIST has posted a response which might be worth a read.
Edit: added links to djb’s original post
deleted by creator
They did it before and they’ll do it again.
I wish I could understand that math in that thread.
I have great respect for djb, but he was an ass here.
Thanks for that link - this whole story is massively overblown clickbait.
The second link has replies that even say the OPs link contains conspiracy theory. The discussion there is better than all else, IMO.
Note: not denying Dan’s claim as I’m not an expert here, just reiterating what I’m reading.
Yeah - at the very list it shows that this is more “reasonable people disagreeing about a detail” than it is “OMG THE NSA IS DESTROYING CRYPTO!”
I mean, DJB does mention NSA has more involvement over NIST than he expected, but that also doesn’t mean their would be collaboration.
In my non-expert reading, NIST made it seem better than it was, DJB disagreed but overestimated how bad it was, and NIST “sort of” said “yea OK we may have bragged.”
Either way, DJB is right to call out something being weaker than it should be. False confidence in encryption is about the worse thing that could happen in the digital age.
Yeah - DJB definitely has a point to make and deserves to be listened to. But “Mathematician has questions about crypto complexity guidelines from NIST” isn’t click-baity enough.
If this is true, NSA might be shooting themselves in the foot when they inevitably have to deal with Russia and China.
Just a guess, but I think they’re less concerned about the giant country’s surveillance of us, and more concerned about not being able to surveil the little terrorist cells.
or you know conversations with your healthcare providers
or the company VPNs of other continents.
They probably consider that they overall lose more with strong cryptography, than the risk of other countries intercepting US communications. They must have other solutions in place to protect confident information. But they likely struggle with encryption being so widely used by anyone. Even granmas can now cover their communications without much effort
From what it sounds like, he’s not saying the algorithm is compromised itself, but rather that NIST is recommending a weaker version of it as sufficiently safe at (possibly) the request of the NSA. If that is the case we would know for sure pretty quickly once DISA updates their STIGs for internal use to include quantum resistant encryption. If the STIGs say to use a stronger version than NIST recommends then he was right.
And who is surprised by this? This is basically the NSA doing their job, nothing else.
We’re not surprised but we do need to mention this, discuss this, people need to be aware. You won’t see much of this in mainstream media except: “And here’s why the end of encryption might be a good thing…”.
Sort of. They’ve worked in mysterious ways over the years. They fucked with DES back in the day (specifically, the S-Boxes, which are big tables of data used during calculations), but evidence since then suggests that they actually improved it. However, they also seem to be responsible for keeping the key length short, which meant it was inevitable that computers would eventually be fast enough to break it (which it was by the mid to late 90s).
The NSA has a dual job. They want to break encryption, but they also need to protect US secrets. Since industrial espionage is a thing, that extends to protecting the secrets of private sector companies. So they sometimes want to improve encryption, and sometimes want to put in backdoors. If you call up someone in the NSA, there’s no guarantee the person your talking to will be on your side or not.
Fortunately, cryptography in the public space has advanced substantially since DES was invented.
They fucked with DES back in the day
Yep. I remember. IBM thought they had something new and BIG, and then came the NSA and just substituted some S-Boxes without comment. And boom, the key space got smaller.
The NSA has a dual job. They want to break encryption, but they also need to protect US secrets.
For them it is sufficient when they can happily read along.
Hopefully we work around this, encryption is more important now than ever.
Doesn’t the existence of key collision help? If you throw a quantum brute force algorithm at a ciphertext, wouldn’t you get a long list of keys, all of which authenticate and appear to work, but for all but one of those keys, what it decrypts to is garbage?
Authentication itself is fucked, but encryption is only heavily weakened rather than completely destroyed.
Yeah but that’s precisely the problem. Cut the list down to say a million choices vs quadrillions, and have a regular lower power server work through that much smaller list.
Don’t forget, this is gen 1 of the quantum systems as well… Who knows what the future holds. Better to make the lock strong now.
Removed by mod
what does this have to do with fascism? that word has lost all meaning
Goddamn fascists and their…
Shuffles deck of cards
…computers!
Because they’re doing it to spy on Americans.
#WordCrimes?
There is no such thing as unbreakable encryption. If you want to hide a message, hide it at the source with the way you phrase things. I still have to buy weed illegally, and I use Signal, but I don’t tell the person I buy it from, “hey, I want a half-ounce of weed and I’ll pick it up on Friday at 2 pm,” I say something like, “hey, are you free this weekend?” And then they’ll say something like, “yeah, do you want to get your usual thing?” and then we’ll arrange a time.
And yes, I see the irony about talking about buying weed illegally when someone could potentially find out who I am on Lemmy.
…there very much is practically unbreakable encryption. We use those every day (it’s part of the s in https).
And your example is just a very rudimentary form of encryption that is far far weaker than the typical encryption methods used on the internet today.
It’s unbreakable until it isn’t.
I think you vastly underestimate modern encryption. I would recommend looking up concepts and math from encryption, it makes more sense for why thinking that practically unbreakable encryption is very much possible once you do.
It’s why governments want to implement back-doors, because they are not actually capable of breaking it more directly.
Did you not read the article? It has nothing to do with backdoors.
…it’s literally about accusing NSA of trying to implement back-doors for quantum resistant encryption.
I have no idea what you’re trying to get at.
NIST is giving incorrect information. That will not enable back doors. And it is only a matter of time before that doesn’t matter. I have no idea why you think there is such a thing as an unbreakable code that is not a one-time use code.
Edit: ACCUSED of giving incorrect information.
I have no idea why you think there is such a thing as an unbreakable code that is not a one-time use code.
I have no idea why you think there isn’t. Maybe you’re going off a strange definition of “unbreakable”. When it’s used in cryptography, it means “unbreakable in reasonable time limits” (e.g. millions of years).
The thing about good encryption is that it’s not just hard to break, it’s mathematically too hard to break even if your available computing power keeps rising exponentially. Unless there is a mistake in the algorithm, it is for all intents and purposes, unbreakable.
There are theoretical limits to the speed of computation. One limit is the minimum amount of energy it takes to flip a bit. For 256-bit encryption, you have to start saying things like “assume we can convert 100% of the energy from a supernova into a theoretically perfect computer with perfect efficiency”. This is a round about way of saying “impossible”.
We’ve been hammering AES and RSA for decades now, and we haven’t been able to get significantly better than brute force against either one. Quantum computers will break RSA (if they can be made with enough qbits, but might be infeasible), but worst case scenario for AES is that we double the key length and we’re good again.
As my grandfather was wont to say, locks are for honest people.
Most forms of security are theater and used as a deterrent.
If your door is locked, and your neighbors isn’t, well your lock deterred them.
Then again, if someone means you in particular harm, they’ll get in, bricks are cheap and most home windows are focused on limiting thermal transfer, not being overly durable (say under an attack). It may not be quiet, you may be able to defend yourself or run or whatever, but the lock was not a deterrent.
So yes, lock your doors, encrypt everything you can, keep devices updated, etc. But it won’t stop a determined bad actor if they have reasonable capabilities to do you harm.
The problem with security, especially cyber security, is that you have to find a medium between secure and usable. Most companies, in my experience, tend to loosen security in the name of usability.
I’m not an expert, but I’m studying in that direction with my limited free time (and more to the point, energy and mental health)
True, and a good social engineering hack will get you wonders quite often.
I hate the term social engineering. The only reason that social engineering is an issue is because security has gotten so good, that now people are the low hanging fruit.
True encryption does exist, it’s just that the encryption key is equally as long as the message itself which shows how impractical it is: if you have a method secure enough to send an encryption key of length X, why not just send the actual message of length X?
That’s interesting. I’ve never heard that before. Do you have more information I can read about somewhere?
Is that what they’re talking about?
Yes
But one-time pads aren’t impractical like they said?
One-time pads are impractical because the sender and the target need to meet up beforehand and agree on a code, and no one else should know this code. With modern encryption, this is not necessary. The target can come up with both the encryption and decryption algorithms, and send only the first to the sender publicly.